Keylogger: Funktionen und Erkennungsmethoden • Technische Umsetzung von Keyloggern unter Windows • Schutz vor Keyloggern mit
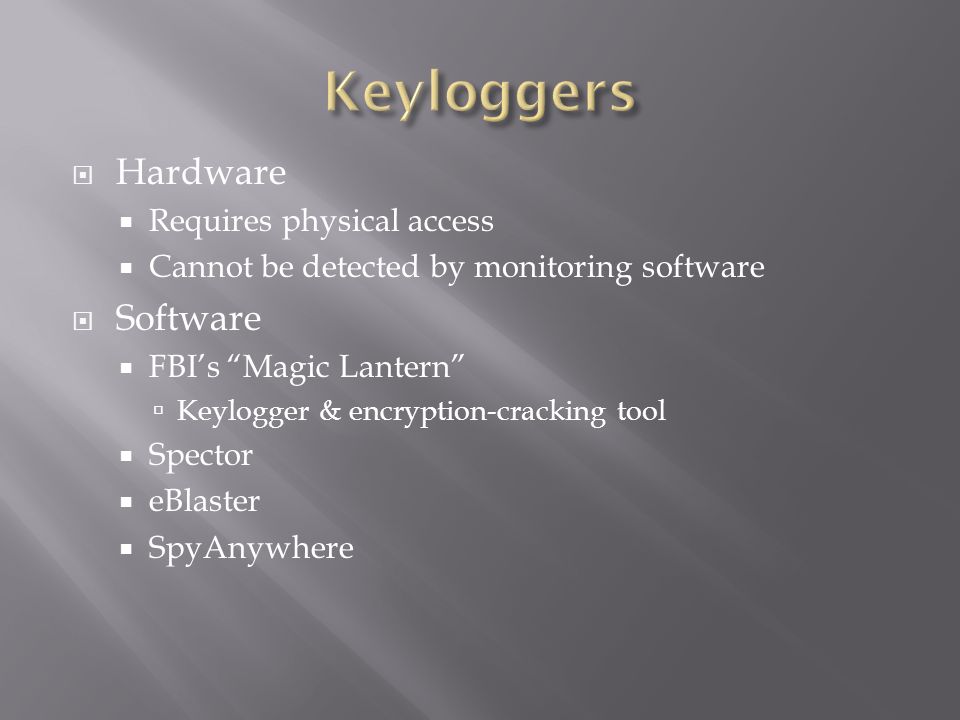
Chapter 4 System Hacking: Password Cracking, Escalating Privileges, & Hiding Files. - ppt video online download

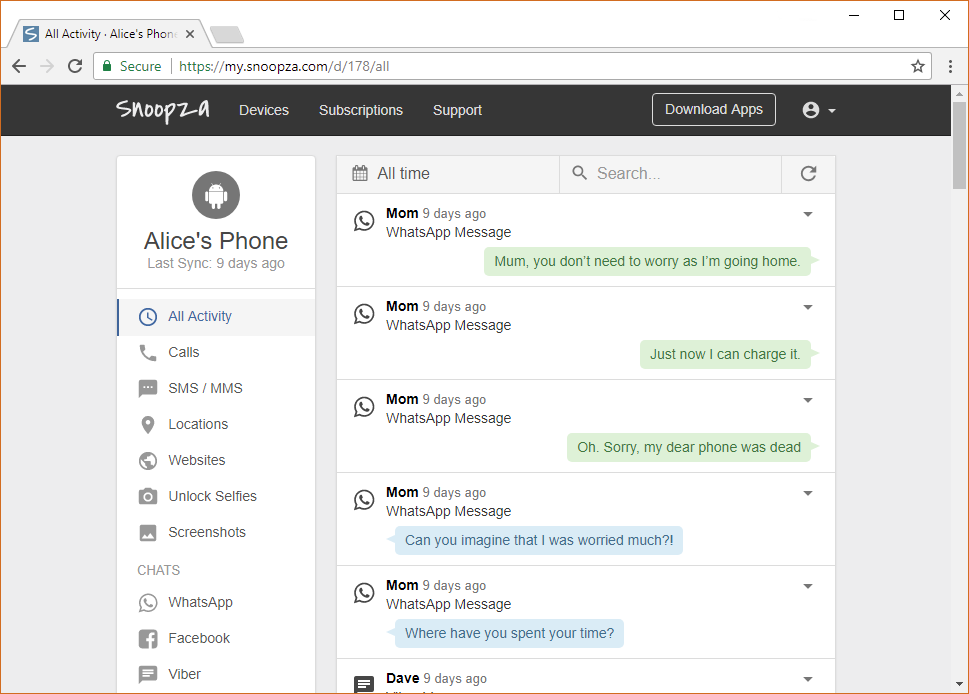
keyloggers.pdf - Chapter 6.5 Keyloggers Introduction • In cases of online identity theft, keyloggers play one of the most important roles in the actual | Course Hero